Two-thirds of hotel websites are inadvertently leaking guests’ personal data to third-party companies according to Symantec. The report found that hotel sites could potentially allow others to view personal customer data, despite the recent GDPR legislation. This apathy to internet security not only puts personal information at risk but could adversely affect the hotel’s reputation. Jason King, Head of Development at LEWIS, gives his view on five steps to upgrading the security on a website.
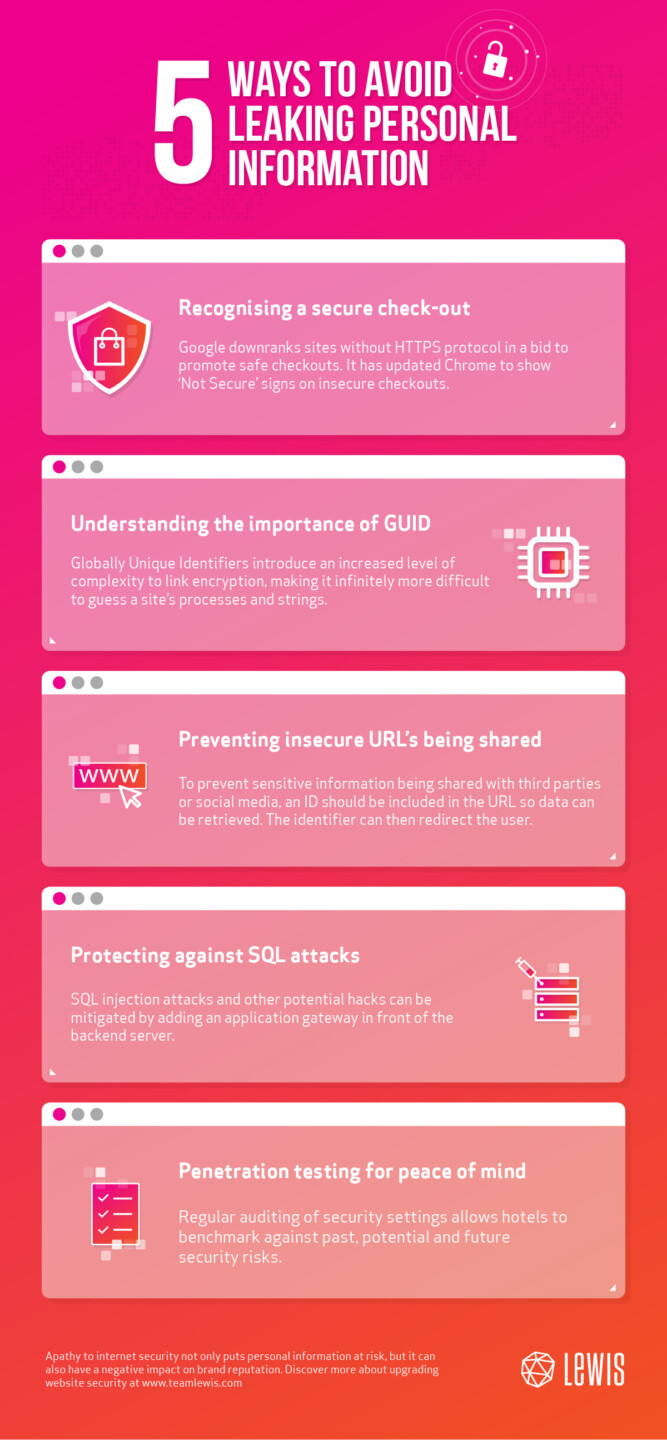
1. Recognising a secure check-out
Google began actively downranking sites without HTTPS protocol from search results in July 2018. It also updated its algorithms so that Chrome users receive a ‘Not Secure’ warning when a site is still using the HTTP protocol. The warning could tempt users to leave the site, negatively impacting a site’s bounce rate and reducing affiliate clicks or e-commerce sales. So, why is HTTPS important?
HTTPS protocol ensures that users are talking directly to the server that they expect to be talking to. And, more importantly that content exchanged between the browser and the site cannot be intercepted or changed from the user clicking on a link and the server presenting the information. This problem is not isolated to the hotel sector, the LEWIS Global Marketing Engagement Index 2018 found that 6.5 per cent of global companies are yet to upgrade. This is despite the recent GDPR legislation making it a legal requirement.
It really is a no brainer considering SSL certificates can now be issued for free.
2. Understanding the importance of GUID
Introducing an increased level of complexity to link encryption makes the ability to guess a site’s processes and strings infinitely more difficult. The most common way to do this is by using a Globally Unique Identifier (GUID) or Universally Unique Identifier (UUID) instead of a numeric identifier.
GUIDs or UUIDs are 128-bit integer numbers that can be used to identify information. Using this method to generate numbers provides hotel chains with near certainty that the identifier cannot be guessed.
3. Preventing URL’s from being shared
Hotels want to make the checkout process as smooth as possible, so they don’t want to force the customer to create an account. In order to send the user a link in the confirmation email so they can view their booking, an ID needs to be included in the URL so the data can be retrieved. To prevent this URL being shared with 3rd parties or social media, the server should store the identifier in a cookie and redirect the user. This means 3rd party tracking scripts won’t inadvertently share the original URL as part of the referrer.
4. How to avoid SQL injections
In modern cloud hosting platforms, SQL injection attacks and other potential hacks can be mitigated by adding an application gateway in front of the backend server. These are relatively easy to setup and are regularly updated to protect against new threats.
5. Audit and penetration testing
Regular auditing security settings allows hotels to benchmark against past, potential and future security risks. Audits will include information handling processes, network, data and access related items and many other elements to look at over security of your digital ecosystem.
Security auditing can be taken a step further through the introduction of penetration testing. This can be done using multiple approaches to attempt to breach a site’s security. The benefits of this are great, providing in-depth insights into how vulnerable a site might be and what the weaknesses are. And, most importantly how they could be fixed.
So how do the top hotels in Spain measure up? We analysed the top 15 hotels by 10 crucial categories, including security. Download the report here.



